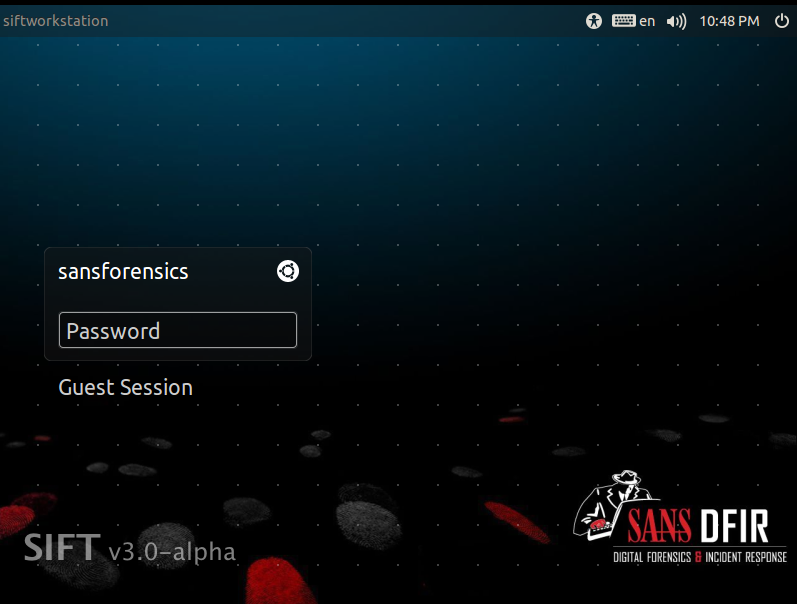
SANS Digital Forensics and Incident Response Blog | Investigate and fight cyberattacks with SIFT Workstation | SANS Institute
SANS Digital Forensics and Incident Response Blog | Digital Forensic SIFTing - Targeted Timeline Creation and Analysis using log2timeline | SANS Institute